


The Most Important Type of Data That No One Is Thinking About
- 2 Mins
Confidential Business Information (CBI) is the information that is unique to the corporation that owns it. It’s anything key to the business that the company would not want its competitors or the public to know. It’s the information contained in board meeting presentations, go-to-market plans, client rosters, contact details, or any metrics and analysis about company performance or future business plans.
CBI represents the majority of a business’s value, and while corporations rigorously protect it in scenarios outside of litigation, it can often take a back seat during litigation. Why is that? And how can corporations prevent CBI from walking out the door? This was the topic in the recent ACEDS webinar, “Confidential Business Information: The most important type of data that no one is thinking about.”
Representing corporation, law firm, and ALSP points of view, the webinar included the following expert panelists:
- Lauren Guillen, Senior Project Manager, Phillips 66
- Jonathan Polak, Partner, Taft
- Brandon Hollinder, VP of eDiscovery and Cyber Solutions, Epiq
Why is CBI often overlooked during litigation?
This was the first question the panelists addressed, and they agreed it’s often due to:
- Competing priorities – where the primary focus is centered around other legal issues (like privilege).
- A lack of involvement of stakeholders who are aware of, and knowledgeable about, the form and presence of CBI.
- Employing outside counsel to review this information can be cost-prohibitive.
- Lack of coordination – there are many stakeholders in litigation (outside counsel, inhouse counsel, vendor partners, litigation support teams etc.) who all may have roles or responsibilities that touch CBI, but none of them own all aspects of defining and protecting CBI.
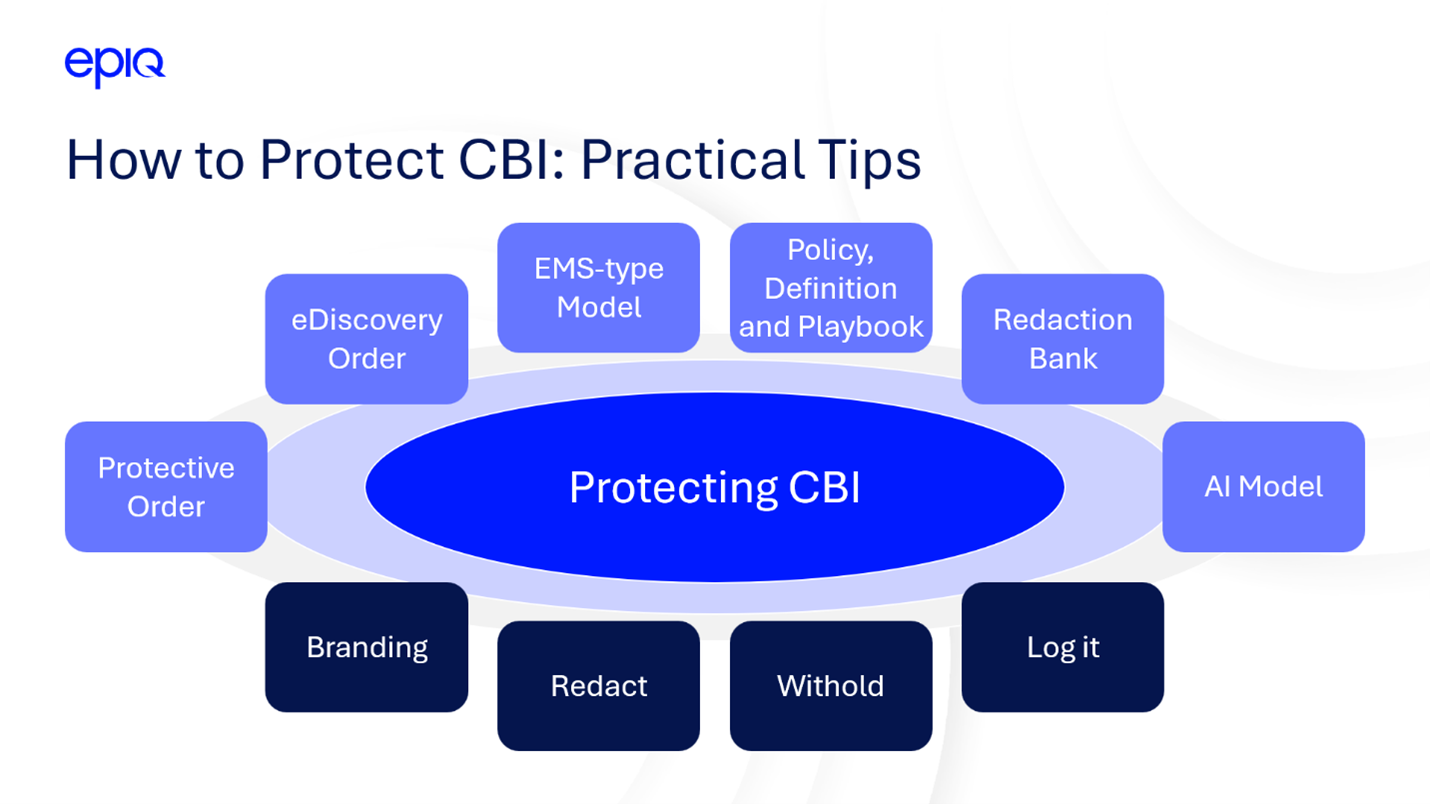
Practical tips and guidance for protecting CBI
A large part of the discussion focused on a set of primary protection recommendations introduced by Brandon Hollinder, including Protective Orders, eDiscovery orders, Managed Service models, Policies, Playbooks, Redaction Banks, and using AI models.
Jonathan Polak commented on his experience with protective orders, “A protective order typically is entered at the beginning of the case. It governs the disclosure and use of documents considered either confidential or Attorneys’ Eyes Only. If documents are produced in litigation that a protective order does not protect, that information could find its way onto the internet, and it may be found on social media. It’s necessary to have the conversation on the levels of protection and set ground rules at the beginning.”
Lauren Guillen discussed how these types of protective orders are followed, as well as the processes and workflows her team at Phillips 66 has in place, “The most common practice (on patent cases) is using the Attorneys’ Eyes Only confidential designation. We can withhold the entire document, tag it as privilege, and the privilege assertion reason would be business proprietary.”
Lauren added further, “That would eventually go on a privilege log, we’d then have the ability to endorse, withhold it in its entirety, and the final option we utilize is redaction.”
Brandon Hollinder commented, “From a supplier perspective, it’s important that documents are properly labeled, branded, and searchable so they can be easily identified.
Otherwise, it’s very difficult for us as the supplier and the receiving corporation to adhere to the policies in place. This includes identifying the designations in the production load files you provide to the party receiving your productions so that they can segregate the documents without actually looking at them.”
How you can get started protecting CBI
The webinar discussion ended with some advice on the most important places to start if you’re just starting to think about protecting CBI.
Jonathan Polak commented, “Having a protocol, a system that’s set up to quickly identify what is worthy of confidential or AEO (Attorneys’ Eyes Only) treatment, and having it be consistent across multiple litigations is key. Building up a database is important, as is talking with people who have experience getting good forms and policies in place.”
Lauren Guillen added, “We have an entire enterprise discovery process that we use, not only on CBI, but all our matters and on all types of data. I’d highly recommend investing in a process, documenting procedures, and making sure it’s repeatable. It also must be flexible. When you build flexibility into the process it’s going to make your discovery more defensible, and you’ll have these conversations at the beginning of every case.”
Finally, Brandon Hollinder discussed how ALSPs like Epiq can provide support, “If you get a protective or eDiscovery order, feel free to send it to us. We’ll see information included that isn’t compliant or won’t make sense with the technology we’ll be using in a case. When we review an order before signature, we can remove any issues and ensure it checks the technical boxes.”
Whether you’re in early stages or have advanced practices protecting CBI, this webinar discussion provides relevant lessons and insights. Watch the full recording here.
The contents of this article are intended to convey general information only and not to provide legal advice or opinions.
